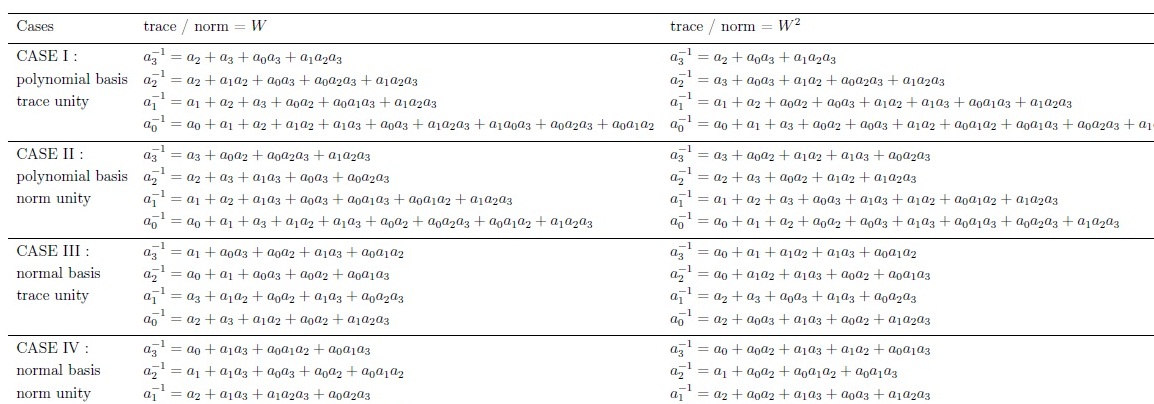
This page supplements our research output presented in M. M. Wong et. al. "Composite Field GF(((22)2)2) AES S-box with Algebraic Normal Form Representation in the Subfield Inversion", IET CDS, 2011. We exploit the Algebraic Normal Form (ANF) representation in the subfield inversion over GF((22)2) to improve both area reduction and performance improvementation in composite field GF(((22)2)2) AES S-box. This is done by converting the GF((22)2) inversion into several logical expressions, without violating the functionality of the circuit's algorithm. The conversion is performed through individual deduction of each of the bit's inversion in the field element. For instance, taking an element of GF(24) as a = {a3 , a2, a1, a0} , hence its inversion a-1 = {a3-1 a2-1 , a1-1 , a0-1 }.
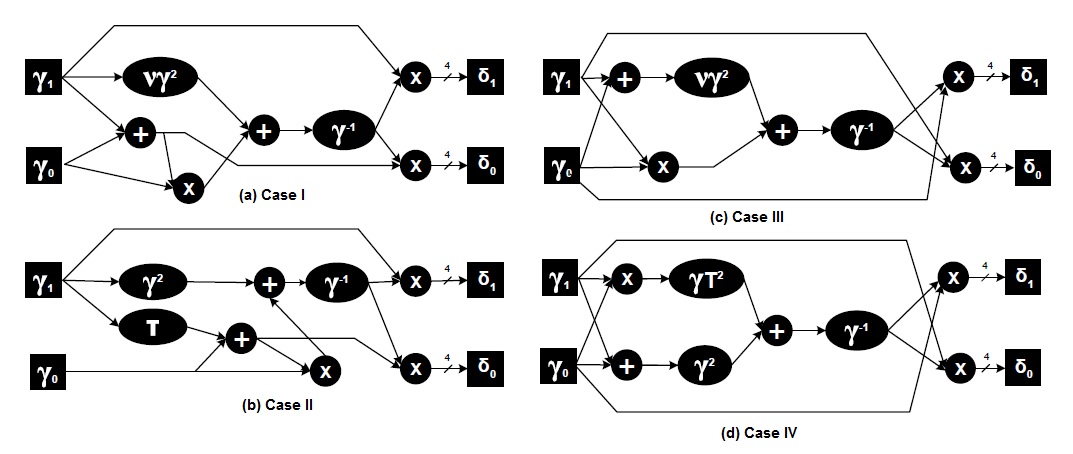
Basically, We can classify the GF(((22)2)2) AES S-box into four general architectures:
where
Case I: Using polynomial basis representation with field polynomials' traces equal to unity
Case II: Using polynomial basis representation with field polynomials' norms equal to unity
Case III: Using normal basis representation with field polynomials' traces equal to unity
Case IV: Using normal basis representation with field polynomials' norms equal to unity
While there are two possible values (W and W2) for the trace or the norm of the irreducible polynomial over GF(24) (and setting one of them equal unity), two detailed implementations for
each of the four architectures are offered. Hence, a total of eight different ANF GF((22)2)
inversions are derived and listed here below.
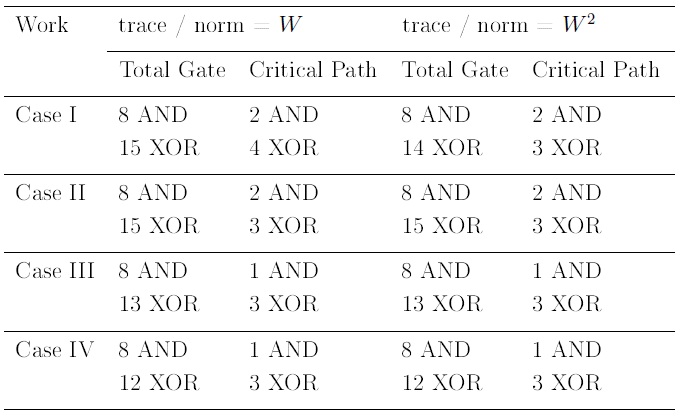
Through sub-structure sharing optimization, the total gate count and the respective critical path for each circuitry is tabulated in this table below.